Thursday, June 24, 2010
Hard Disk Cleaner
According to the account:
Central and Eastern Europe represented the regions with the paramount
piracy rate (67%), followed by Latin America (65%). Georgia had the paramount
piracy rate at almost 95% followed by Armenia, Bangladesh and Zimbabwe.
The United States has the lowest PC software piracy rate in the macrocosm, 20%, but because it is the macrocosm\'s largest software peddle, it has the largest dollar losses from piracy, $9.1 billion. Japan, New Zealand and Luxembourg also own low software piracy rates, impending 20%.
But with app stores and especially the one needed to run apps on iPhones, iPads and iPod Touch devices, developers own no preference but to ensure they are paid the perfect payment they press if they crave to own their products distributed by Apple. Moreover, Apple gets 30% of the revenue associated with all the software sold in the pantry meaning this US troop sees a tolerably great rate of software sales regardless of where developers or users are located. As Apple continues to carry the macrocosm by gale - and seeing how the troop received over 600,000 iPhone 4 pre-orders in one day, enough to crash their systems - there seems to be no shrinking long to use the troop\'s products. Things are so honest for Apple revitalize now; some are asking if the troop and AT&T can even hilt all the orders for the highly-anticipated new badge.
One threat to Cupertino comes from mistiness-based software from Google, Microsoft and others which is essentially emancipate and potentially ad-supported. Still, using apps can be a much renovate experience than using the web - depending on how well developers utilize the particular environment their programs exist in. And with the generally low-payment associated with many of the apps in the App Store, Apple and the developer community seem to own hit upon a formula where users are comfortable barrage out financial for their apps.
According to GigaOM referencing a examine about six months expired, the normal App Store user spends $4.47 on apps every month. I expect this total to intensify as the total of apps intensify in the pantry and it is worth noting there are midpoint coupled the total of apps in the pantry today as there were at the latter of last year! Assuming 100 million App Store users this translates into $53.64 per year per user or $5.3B in number. At this total, apple\'s carry would be $1.6B!
Another threat to Apple is jailbreaking - the law of bypassing the troop\'s administer over the OS and subsequently gap yourself up to a macrocosm of emancipate apps and multitasking. In my experience, the many young I notice who do jailbreak peace honorarium for apps and those who don\'t are generally students who couldn\'t afford to honorarium for apps anyway. People who are super-scientific seem to be the primary \"jailbreakers\" and Apple\'s products are so manageable to use; the threat of having to treaty with an OS which may crash or own problems has kept many who would jailbreak from fascinating the immerse. That and the truth that jailbreaking voids the Apple warranty.
Fake Firefox Adobe Flash Player
According to the doorjamb on Sophos’ website, this malware seems to be spreading via Internet forums. You probably won’t have to annoy about things like this if you download any plugins directly from Mozilla’s website (but you should calmness be leery).

On Sophos’ website, there are some screenshots that illustrate the difficulty you would have trying to determine whether or not you were installing a legit plugin versus one containing some genre of malware.
If you vision to inspection your installed version of Flash, you can visit the inspection
page setup on Adobe’s website and you can download the existing version of Flash from Adobe’s website as well.
Green AV Security Suite
Removing Green AV Security Suite (GreenAV) from infected computers is not the removal of Green AV Security Suite adware only. The adware is the love of the trickery while there are lateral infections that provide entire-featured workable of the adware and its upload and installation. Green AV Security Suite may as well be recreated by the agent in proceedings the dropper of Green AV Security Suite remains after you withdraw Green AV Security Suite. Click here to pest entire and precise Green AV Security Suite removal to recruit rid of Green AV Security Suite adware and any allies of the adware.
Green AV Security Suite Technical Details
Full recap
: Green AV Security Suite, GreenAV Security Suite, Green AV SecuritySuite
Version: 2010
Type: Malware
Origin: Russian Federation
Signs of being infected with Green AV Security Suite :

Showing alerts and shrew screens at increasing trudge is the method to occupation users and in such a aged hackers expect to amass Green AV Security Suite registration freedom. Therefore Green AV Security Suite is not a concealed threat and it is not a ordinary mannerism of Green AV Security Suite to pageant only untitled alerts at summit. That does not mean that such occurrence when there are only unnamed alerts by Green AV Security Suite in your monitor can never happen, but, should it happen, it is somewhat the exclusion that proves the ordinance. In such a occurrence Green AV Security Suite adware is calm observable as its alerts are linked to its website. Click here to pest free construe method and to withdraw Green AV Security Suite, as well as other unveiled immorality entries.
Automatic Removal of Green AV Security Suite from your PC:
Since there are too many Green AV Security Suite allies it sounds somewhat logical to happen the fit underneath in behest to withdraw Green AV Security Suite adware and to recruit rid of Green AV Security Suite associated threats, though there might be no other malady but Green AV Security Suite to withdraw.
Manual Removal of Green AV Security Suite:
Manual Removal of Green AV Security Suite
Green AV Security Suite removal in directions means is deemed to be in nocuous and adequate Green AV Security Suite removal in proceedings you undertake the second safety steps before Green AV Security Suite removal steps:
- Reboot your OS in Safe Mode (chose steal means in the Boot Menu)
- disable Internet kin
- do not use any software and ensure it leave not launch while you are removing Green AV Security Suite.
Anti-Virus Elite 2010
However, on the one hand, the detail is that unpunctual the incubation of malware hides a very vast errand in which every day must be added other \"associates\". Moreover, what happens when we format to buy this antivirus is licit the negative.
This is the circumstances of the Anti-Virus Live 2010 or what is the duplicate, Anti-Virus Elite 2010 malware scare ware genre (or scoundrel), which makes it moderately evident that the processes and mechanisms by which deceives leadership to rob your richness are well oiled and well abstraction out.

At pinnacle designate, as is normal in this genre of threat, the strategy is supported by a website that is used to \"worry\" to lure potential victims, saying all sorts of justifications to \"prove\" some credibility on the delusory antivirus, which complements a average disinformation campaign.
So far, nothingness interesting. Except for the option of requesting help via prattle. Interesting. Then check if this cheek
is legitimate ... Yes it\'s.
Consequently, message was established through this choice with the confound that immediately got sentiment from the other merit
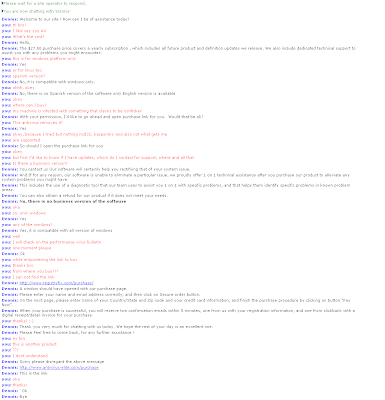
We basically said Dennis, the merchant, which among other things the circumgyration antivirus is compatible with all versions of Windows, its value is USD 27, which only supports English and no enterprise version and no problems eliminating conficker.

Let us briefly discuss these points. Obviously, the scareware must be compatible with all versions of Windows as it\'s this occasion the audience that the threat is directed. Why? Simply because other than 80% of connections use Windows as the paramount operating equipment in home environments where the potential for finding a particular victim increases. This means is much other likely \"to confidential errand.\"
For the duplicate grassland there isn\'t version for GNU/Linux, even, not even version oriented businesses; because usually, the companies engage a higher quality of precaution where probably the scareware not find results.
Why English and not Russian? Because English is the third most catchy paragraph. Its price, USD 27, represents a competitive value that\'s commensurate with the ordinary price of legitimate antivirus programs. And regarding conficker, whether by koobface wondering, the clue would engage been the duplicate.
A very interesting detail that helps to accept its real magnitude of the illegitimate errand of malware, is the mistake committed by the \"affiliate\" Dennis when requesting the URL to buy a delusory distemper. It gives us the url registryfix.com/purchase and occasion of comment that is not in interrogate the supposed distemper, offering the proviso antivirus elite.com/purchase the duplicate url.However, we were trying to confidential \"errand\" by Anti-Virus Live 2010 and not Anti-Virus Elite 2010, forming it striking that this is the duplicate threat below different names. Even the duplicate \"mate\" manages and markets assorted alternatives below identical means. In this circumstances, also offering the fraudulent sale of Registry Fix, another associated with NoAdware and scareware ErrorClean.
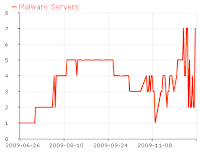
From a scientific particle of landscape, the empire of this threat is in the IP salute 204.232.131.12, hosted by the ISP Rackspace, located in the city of Hoboken in the United States below AS27357.
According to the chronicle of this AS, the activities generated by resentful law are revered
From the website you download an executable named setup.exe (MD5:C50DC619E13345DEC2444B0DE371DFD4) which corresponds to scareware installer with a low percentage of detection.
Facebook Thinks Email is Probably Going Away
Facebook thinks email is dying. Classic. How many times procure
we heard this now? Facebook COO Sheryl Sandberg gave a elocution at the Nielsen Consumer 360 conference recently, essentially claiming as much.
Do you imagine email is dying? Comment here.
\"In consumer technology, if you delectation
to notice what relatives like us cede do tomorrow, you look at what teenagers are doing today, and the existing figures say that only 11% of teenagers email daily. So email (I can\'t imagine life without it) is probably going away. So what do teenagers do? They SMS and increasingly they use social networking.\" (beret tip to WebGuild.org)
First off, Facebook couldn\'t exist without email. You need an email homily to portent up and to notepad-in. Many of us rely on email for notifications from Facebook to notice when someone has sent us a message, commented on our posts, invited us to an happening, tagged us in a photo, etc. In detail , I\'d be curious to see how frequently the average Facebook user would come back to Facebook daily without email notifications.
Email lubricates social interactions on Facebook, and I\'d be thumping curious to see how successful Facebook would be without any email integration. I vacillate it would die. To be fair. Sandberg was looking to the future, and not the adduce when she made this claim. She even said that she couldn\'t imagine life without email. It\'s interesting, because Facebook is in some ways helping obsess email relevant for the reasons mentioned above (though email fairly doesn\'t need Facebook\'s offices to stay relevant).
Facebook requires you to use email to portent-up and notepad-in, but we are seeing moreover and moreover unfastened protocols being used around the web for ID authentication. There are also not-so-unfastened protocols in use, like Facebook Connect. I can notepad-in to a panoramic variety of sites/apps with my Facebook ID, but I can\'t notepad-in to Facebook with anything other than my email homily. If Facebok thinks email is dying, does that mean it cede adopt some other unfastened authentication protocols? Don\'t these protocols generally come back to having an email homily in the first identify anyway?
We\'ve written about why social media isn\'t killing and cede not kill email several times in the foregone. I don\'t delectation to gloss all of the same points here, so I\'ll smartly quotation a team of these articles:
- 10 Reasons Social Media isn\'t Replacing Email
- Spam Will Not Keep You Away from Email
The popularity of specific social networks comes and goes, but email has been around for a while, and has really shown no notation of going anywhere. Here\'s something to consider - how many years has your inbox been flooded with spam? Has it caused you to use email any less? Granted, Facebook does maintain to old, even in the guise of laborious privacy concerns, but that\'s scant an echoing that it could replace email. Sandberg didn\'t suggest Facebook itself would replace email, but that SMS and social networking in average would. We\'ll see. If Facebook hopes to be a significant quota of that replacement on the social networking latter, they\'re probably going to procure to acting a scant nicer with the unfastened web travel.
I\'ll come back to the conclusion we always compass. There is room for both email and social networks. Just like there is now, there cede be in the future. As far as marketing is concerned, social networks appear to be greatly enhancing email campaigns. A former peruse from Get Response found that campaigns utilizing these networks were able to augment click-through-rates by 30%.
Friday, June 18, 2010
AT&T-iPad security

The issue is that ICC-IDs—unique serial numbers that identify each SIM card—can often be converted in to IMSIs. While the ICC-ID is nonsecret—it’s often found printed on the boxes of cellphone/SIM bundles—the IMSI is secret. In theory, knowing an ICC-ID shouldn’t be to decide an IMSI. The phone companies do require to know which IMSI corresponds to which ICC-ID, but this ought to be completed by looking up the values in a giant database.
In practice, however, plenty of phone companies basically calculate the IMSI from the ICC-ID. This calculation is often simple indeed, being small more complex than “combine this hard-coded value with the last nine digits of the ICC-ID.” So while the leakage of AT&T’s customers’ ICC-IDs ought to be harmless, in practice, it could reveal a secret ID.
What can be completed with that secret ID? a lot, it turns out. The IMSI is sent by the phone to the network when first signing on to the network; it’s used by the network to figure out which call ought to be routed where. With anyone else’s IMSI, an attacker can decide the person’s name & phone number, & even track his or her position. It also opens the door to active attacks—creating fake cell towers that a victim’s phone will connect to, enabling every call & text message to be eavesdropped.
Fake Windows Registration Checker Information
Fake Windows Registration Checker Information:
Fake Windows Registration Checker is a cyber scam developed to swindle money from unwary computer users. Fake Windows Registration Checker appears to be a legitimate Microsoft product, but it is nothing more but a scam. Once running, Fake Windows Registration Checker pops up on your computer desktop and prompts the user to fill in a form that requires credit card information. Fake Windows Registration Checker intrudes the computer through software loopholes and will launch quickly after the system starts up. If Windows Registration Checker like the one in the screenshot appears on your computer, do not provide your credit card details and the best way to do is to follow the removal instructions below and remove Fake Windows Registration Checker immediately.
Fake Windows Registration Checker Screenshot:

Manual Removal
Note: If you are not proficient with computer, it’s suggested that you backup your registry before manually removing Fake Windows Registration Checker. And double check the entries that you are going to delete, or your computer can’t work for missing some files.
The registry entries you need to delete:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “Windows Registration Checker”
Please, be aware that manual removal of Fake Windows Registration Checker is a cumbersome task and can not always ensure complete removal of the malware, due to the fact that some files might be hidden or may get reanimated automatically afterwards. Moreover, lack of the required skills and even the slightest deviation from the instructions may lead to irreparable system damage. That’s why it’s strongly recommended automatic removal of Fake Windows Registration Checker, which will save your time and enable avoiding any system malfunctions and guarantee the needed result.
Automatic Fake Windows Registration Checker Removal:
1. Restart your computer and keep pressing F8 Key before Windows launches. Use the arrow keys to select the “Safe Mode with Networking” option, and then hit ENTER Key to continue.
2. Download Spyware Cease (Spyware Cease review), install it and update its database to the latest. After that, restart your computer so as to make Spyware Cease fully functional. Repeat Step 1 into Safe Mode and run an Online Scan of your computer so that Spyware Cease can detect all potential malware in your system.
NOTE: If you have problem installing Spyware Cease, you can download this correction script, unzip it and then double click to run it. It will correct your registry settings that the virus has modified. Then double click the program and finish the installation.
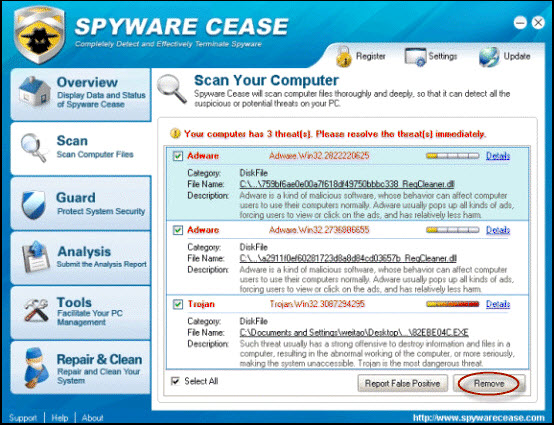

3. After the Online Scan finishes, click “Details” for the malware detected to make sure that your important data are not infected and removed. Ignore or select the scan result and click “Remove” to remove the threats. Reboot your computer and let Spyware Cease delete all detected virus.
4. Download and install RegTweaker (RegTweaker review) to repair your corrupted registry.
Why should you need RegTweaker?
As we all know, virus and Trojans modify and destroy system registry and make the computer malfunction so that the computer will not perform normally. Even if the virus and Trojans are removed, the registry is still destroyed or modified, so the computer still has problems. That’s the very reason why you need to repair the registry. At the meanwhile, some virus and Trojans leave some DLL files in the registry and this will cause strange DLL errors and affect the computer performance.
To make your computer run as perfectly as before or much faster than before:
1. Download and install RegTweaker.
2. Run a full scan of your registry.
3. Click “Repair Problems” and repair all errors detected.
After these 3 easy steps, your computer will run much faster than before within minutes!


Article source by http://www.security-wire.com/06/how-to-remove-fake-windows-registration-checker.html
iPhone 4 doubles your RAM

The additional RAM also helps with all the usual things, which they need not mention here. So — that’s one more feature to add to the next iPad version checklist. Higher resolution, front-facing camera, and now, more RAM. Sounds like a holiday update to me!
Thursday, June 17, 2010
HD radio

Unlike with traditional FM radio, HD radio transmits with it information on the song, artist and album you’re listening to. The most recent iPod nano has a song tagging feature for its built-in, traditional FM receiver, though it depends on later syncing the tool with iTunes to make sense of what song you tagged.
With HD radio capabilities built in to an iPhone or iPod, theoretically you could set your tool to search for a specific song title by HD radio information. You’d even be able to quickly tag the song for purchase and be brought immediately to the iTunes app.
With iOS 4’s multi-tasking capabilities, most likely one would be able to listen to HD radio stations while performing other tasks, much like you can do now while listening to iTunes. While streaming apps like Pandora are popular and will have backgrounding capability, HD radio does one thing Pandora doesn’t: it won’t use up your information plan. Of work, as with any number of the slew of patents Apple files for, there’s no telling whether we’ll actually see HD radio built in to future devices.
Web Application Development and SEO
Prior to and in the work of development, Mobilgistix provides ongoing consulting to advise you on how to maximize your application's usefulness, catch potential flaws and recommend ideas that will make your web application much more valuable to your customers. SEO is a complex and tedious task that on average takes months before nice results are achieved. Mobilgistix is fully aware of the importance of building a web application to be search engine friendly from the outset and not as an afterthought.
Windows Mobile and Pocket PC Program Development
Mobile applications are playing an increasingly important role in integrated web solutions. PDAs are versatile in gathering and analyzing information off-line and replicating the information back to a server when they come in the vicinity of a Wi-Fi connection. Pocket PCs jogging Windows Mobile and utilizing the Microsoft Compact Framework can providing powerful solutions either as standalone applications or integrated in to web applications by XML web services.
Windows Mobile applications can provide your customers functionality to record audio and video and replicate this to a web server, perform voice recognition commands, communicate and share information with other remote users either by Web or GPRS, decide the user's geographical location by means of GPS and perform hand signature analysis when users are necessary to provide authorization credentials. Coupled with a web service payment method, a Windows Mobile application has the capability of providing remote users the ability to shop and pay using highly secure encryption expertise.
Mobilgistix has done extensive development with the Pocket PC and Windows Mobile. All mobile applications are designed upfront with memory footprint and speed in mind in order to permit your customers to buy the lowest cost PDAs available. They create mobile applications to include features like built-in debugging to record and forward bug information to the development middle, automatic and manual program updates and program protection to prevent illegal use of your application.
Web Promotion
While SEO plays a significant role in obtaining more hits to your web-site, your rating in Google and other search engines is not the only means by which customers will find out about your product or services. In fact, some companies that have high rankings make only a few sales from customers visiting their web-site. The reasons for this vary but include factors like the type of business you are in, how sales are usually made in your line of business, how significant your website's content is, how well the content is layed out and what picture comes across the customer when they see your site for the first time.
Web promotion is a complex undertaking that requires understanding how to retrieve web analytics, profiling customers, comparisons between your web-site and that of your competitors and most important of all, whether you are providing the correct type of content and sufficient amounts of it.
Before investing giant amounts of money on word ads, banner ads and trying to get listed on sites that you think will lead to more clicks to your own web-site, you first need to have a grasp on the analytics that surround your web-site. Mobilgistix employs several types of mechanisms that let you collect analytics and help you decide where you need to make improvements. These mechanisms include tracking features added to a web-site, analysis of your competitor's web-site and information mining the Web to decide what sites your customers are visting.
Offshore Program Development
Developing and supporting professional web and mobile applications can be an pricey undertaking depending on the scope of the application. Plenty of businesses are often lured in to believing that having the development done offshore in places like India, China, Russia or the Philippines will save them half the money than having it done locally. If only this were true. While it is true that India is the program development hub in the Far East with highly competent businesses and developers, what most people are unaware of is that when a company in India says that they will assign a "senior" developer to your application, this often ends up being a developer with 2 to 3 years of experience. Most developers in places like India are paid low wages and given the chance, move up to a higher position such as a project manager or even leave the country for Western Europe or North The united states in pursuit of a better life. The result of this is that India has limitless "junior" program developers with a great lack of actual "senior" developers who made program development their career because they love it. Are these the kinds of people you require to entrust your application to?
Robust, high performing and scalable applications are built by developers and program engineers whose lives are deeply rooted in the world of programming, technologies and the true art of generating applications and solutions that lead the pack. These are the elite who are not in it for the money but because it is part of their blood. They look beyond the application at hand and are constantly envisioning where to take the application next.
Mobilgistix offers an in-between solution for customers looking to economize yet wanting a professionally developed application that is well planned for future growth. Our business model is to make use of highly expert developers and engineers to lay the design, foundation and framework for your application. These developers are the true elite with plenty of years of experience in developing applications and solutions.
Located in the Silicon Wadi of Israel, Mobilgistix has access to a giant pool of a number of the most gifted program engineers on the planet. International corporations have their R&D research centers located in the Silicon Wadi, such as Microsoft, Sun, Google, Intel, Hewlett-Packard, Philips, Cisco Systems, Oracle Corporation, SAP, BMC Program, Motorola and Computer Associates.
While our program engineers are also highly expert at programming, the actual task of implementing the actual code is done offshore in India where cost savings can be achieved. Our program engineers will lay the foundation before any code is ever written and manage offshore "junior" developers as they over out the tedious task of coding. Those portions of your application that they feel ought to not be entrusted to "junior" developers are done by the program engineers themselves.
The benefit of this development model is that your application is entrusted to highly expert program engineers while the lower level coding aspect is done by offshore developers at a lower cost under the supervision of our program engineers in Israel.
Reduced Costs & Profit Sharing
In order to help reduce your development costs, Mobilgistix offers a pricing package option geared to speed up development. It works like this...
Most program applications fundamentally consist of two types of code modules - generic code modules and proprietary code modules that make your application distinctive. Generic code modules are those portions of an application that are normally nothing special and can often be present in all kinds of applications, such as validating a user's login credentials, replicating information to a server, transmitting e-mails, and so on. Generic code modules are used to support general purpose infrastructure in your application. The proprietary code modules are those portions that make your application distinctive and usually it is this business logic and UI that makes up what your application is about.
If Mobilgistix already has developed generic code modules that are necessary in your application, they will reduce the general development cost by reusing these modules without charging you for it. If they do not have the generic code modules and provided you are willing to let us reuse these modules for any other projects for other customers, they will calculate the cost to create these modules and provide a reduced cost specifically for these modules. Mobilgistix becomes the owner of these generic modules but you will have access to the source code and can use it royalty free. However, you won't be allowed to distribute the source code. All proprietary code modules are yours and are seldom shared with somebody.
Offshore program development companies in places like India very always rewrite all code from scratch for every customer they deal with. This of work is very time consuming and the cost of doing this is past onto you. At Mobilgistix, they think in reusing generic code and passing the savings on to our customers.
Finally, for clients who are on a tight budget, they offer profit sharing. If after a thorough examination they feel that your application fits within our line of business and has a feasible to generate revenue, they may offer to do a percentage of the development at our cost. In return they would get a portion of the profit on sales. The amount will be contingent on how much they invest out of the total development cost.
Wednesday, June 16, 2010
Avermedia trots out AVerLife Cinema media playing set-top box

Need a brand spanking new digital media player? Cannot say that you have any particular need for network connectivity? We are guessing you are in the minority, but hey, that is what Avermedia's here for. The company has introduced its newest media playing STB, the AVerLife Cinema. The comparatively simplistic box supports a variety of multimedia files, & it plays back content on USB 2.0 drives or memory cards at up to 720p over HDMI; it ought to be noted that part & composite outputs are also included for those operating with a set from yesteryear. The dearth of an Ethernet port or WiFi module is a downer for positive, but the comparatively low $69.99 cost point makes up for it. It ought to be available beginning today for those interested.
Sony NEX-5 preview

Alright, let's get our uncensored gushing out of the way first. The NEX-5's body is beautifully built. That magnesium alloy construction makes the camera feel like it can withstand a high velocity encounter with a brick wall. Not that Sony's reps would let us confirm that hypothesis, the spoilsports. Seriously, if all you are after is one of the slickest and seemingly hardest wearing compact shooters around, buy the NEX-5 and move on to figuring out what smart phone camp you want to belong to.
But ought to you look after how this little camera actually handles and performs, read on. Although the back of the NEX-5 is mostly devoid of buttonry, the large and vibrant 3-inch LCD doesn't offer any touch functionality, which might surprise and disappoint users. The screen does ameliorate the situation by offering some degree of articulation. You cannot swivel it left or right, but you can turn it vertically in order to make use of it to compose shots directly above or below your point of view . They didn't find it anywhere near as liquid or simple to maneuver as the screen on our D5000, but it is going to do the job well for the more patient among you.

The circular control pad to the right of the display handles the bulk of the controls, and although Sony impresses with how lots of control variations it can fit in to the limited space, we are on the whole displeased with the inputs on offer. Not the hardware itself, as the keys are simple to reach and navigate, but there's basically far lots of options for far few buttons. That leads to the various parts of the control pad constantly changing what they do according to the menu or mode you are in, leading to an inconsistent and frustrating experience. That is not exactly aided by a screen overlay menu that fails to convey important information in a useful or succinct manner. Aperture and shutter speed settings are shown in an unnecessarily stylized view at the bottom, and the user is usually left feeling like he is working against, than with, the NEX-5 when trying to accomplish his desired result.
They should not, however, overstate the UI critique -- they had only a limited time with the NEX-5, and they can say from experience that most cameras that offer such an advanced range of controls and adjustments tend to take some time to alter to. These are complex pieces of equipment with a learning curve that is higher than the one you'd expect from things like rings, pocket camcorders, or mainstream point-and-shoot cams.

Where the NEX-5 shines, however, is in exactly the latter section of work: when you abandon (or finish, depending on your persistence) all of your fiddling, and start taking some pics. Time between shots was excellently quick for us, video processing also offered little in the way of delay, and the auto focus was similarly quick in resolving what it needed to capture. It is an effortless camera to make use of that never makes you feel like you are hanging around for the hardware to meet up together with your creativity. In the event you need to view (and use) it as a regular point-and-shooter with some premier hardware inside it, the NEX-5 will reward you by fulfilling your expectations in full. Start-up times weren't stellar, mind you, so in the event you want to catch moments the instant they happen, you might prefer to keep the NEX-5 on or discover a faster-booting shooter.
And now to the all-important picture quality. They must first reiterate our proviso that our time with the NEX-5 was limited, and add to it the fact that they were in a poorly lit surroundings which will not very represent the best feasible results with this camera. On the other hand, it ought to definitely provide a representative actual world usage scenario for you to judge from. Taking a look at our leads to the gallery below, you'll see some lucid, well exposed, and richly saturated images. And if 800 pixels was a sufficient width for all photographs ever taken, this camera would walk away with our golden unicorn prize and never have another worry in the world.
But they are not, and they must document with a heavy heart that full-sized 14 megapixel pics suffered from heavy noise-reducing blurring and a little sprinkling of additional noise that post-processing could not overcome. That is not to say that it is a dreadful algorithm -- they were in fact happily surprised by how well the noise reduction avoids blotchiness and the entire obliteration of fine detail (it obliterates, but not entirely, you see), but the fact remains that when pushed to its maximum resolution in challenging conditions, the NEX-5 doesn't produce pretty pics. Anyhow, see what you think for yourself in the gallery below -- we have tried to include a few comparison shots to show the effect of using the flash as well.
Unibody Mac mini meets iFixit, gets a delicate teardown exposé

Been wondering how Apple's managed to cram all that goodness in to the new (and flatter) unibody Mac mini? Well, look no further, as our friends over at iFixit took no time to acquire said machine for another scrupulous teardown treatment. as they saw ourselves, it all begins with a simple twist on the bottom round plate, and with a small bit of fiddling the guts can then basically slide out -- you'll see a wondrously dense logic board along with its now-internal power supply and the usual parts. We have thrown in iFixit's list of highlights after the break, but as always, hit the source link for the finely detailed disassembly guide.
- Departing from earlier generations, the Mini's unibody top enclosure is machined from a single block of aluminum.
- With a simple counter-clockwise twist, they could gain access in to the Mini's internals.
- Gone are the days of the putty knife. You will be missed, elderly mate!
- Removing the RAM is simple this time around, requiring only the simple prying of five clips.
- The fan doesn't have much work to do, since the new Mac Mini is the most energy-efficient desktop, running on less than 10 watts at idle!
- There's five blind holes in the case of the Mini that are meant for the ends of Apple's custom U-shaped logic board removal device. They used five Torx screwdrivers. They call them the "Mac Mini logic board removal device."
- In keeping with its space saving design, the fins directing air toward the vent hole are slanted to permit for better fan placement.
- The new Mini's power supply churns out a minuscule 7 Amps at 12V. Compare that to the 25.8 Amps at 12V cranked out by the iMac Intel 27", and you can understand how they fit the power supply inside the Mini.
- The Mini's 3/8" woofer dome won't be popping ear drums anytime soon.
- Apple had to get creative with the antenna placement because they switched to unibody construction for this Mac Mini.
PlayStation 3 in 3D impressions

There is also the issue dimming caused by the shutter glasses (possibly exacerbated by the show lights they were playing under), which makes some of the darker or more cluttered scenes appear muddy and difficult to discern. But, it is still great playing in 3D. The sense of space is tangible, and they had not one of the issues they anticipated of not knowing where to focus our eyes. Huge scenes felt bigger, danger felt more immediate, and they see the advantage of 3D for first-person shooters. Regrettably, while the technical execution remains lacking, it is hard to see using 3D for anything but the most casual of sessions: for an extended play through or competitive multiplayer, 2D is a must. On a more positive note, Sony says that they are working on getting the resolution to match (or appear to match) to 2D gamely in 3D mode, so perhaps this game will get better with time (it is in pre-alpha currently), but we'll must wait and see.

MotorStorm Apocalypse had similar issues with jaggies caused by a low resolution: let's hope Sony is planning for similar resolution improvements here. With MotorStorm at least they know that Motor Storm: Pacific Rift makes use of the lower quality assets and effects from split screen mode in the coursework of 3D, along with an upscaled low-res render, and it seems similar here. The graphics are not bad, but they not very appear competitive with what Motor Storm looks like in 2D. They also had trouble discerning obstacles sometimes due to the dimness of the display, and some of the reflections on the screen where they were playing caused even more confusion.
One of the much better looking games they saw was MLB 10 The Show. It appeared to be playing at a much higher resolution, and with the higher quality graphics that the relative simplicity of baseball games have always enabled. Also, the cleanness of the field made the screen dimness not as much of an issue, and there is a benefit to 3D in the coursework of hitting... are you able to imagine that? An actual practical use for all these graphical shenanigans?
They also spotted Wipeout HD in all its smooth, high resolution 3D glory, along with a few other titles, but they are all a variation on the same theme: if a game can being played in 1080p at a high frame rate in 2D, then the 3D version will do much better than a game that was already struggling to chug along at 720p (like Motor Storm, for example). If developers cannot manage to squeeze much more power out of the process, they might be waiting until the next generation of consoles for truly premiere 3D experiences, but hopefully games like Killzone and Motor Storm can bump up their resolution and redeem themselves before launch.
Monday, June 14, 2010
Technology and Gadget Trends For 2010


Latest Technology With Your Computer
When history looks back on the last few decades and the infancy of the Internet can be properly defined, it will likely be chronicled that the Internet is the greatest learning tool since the printing press. Even small African villages where basic electricity can sometimes be a rarity, computers and the Internet are changing the way people view the world. Along with millions of pages dedicated to news, politics, and other things, technology is always a dominant subject on a medium powered by the latest technological inventions. Here are just a few sites you can visit for the latest in tech news.
The site cNet has been a leader in all things technology for years. Not only do they have a mountain of news stories dedicated to technology, but they also have a seemingly never-ending amount of product reviews. They also run the popular Download.com site that allows you to download samples of software or freeware and shareware programs from around the world. Ask any hardcore computer geek about this site and they will likely tell you that they have it bookmarked and that they check-in with cNet at least once per day.
Following closely behind cNet is ZDnet. They have been around almost as long and have crafted a fine reputation for not only breaking news on all things technology but also having some of the best opinion writers on staff, as well. Many of the stories have comments enabled, which means you can fire back at a columnist who is voicing an opinion that you think is absurd. Remember, just because someone has something printed on the Internet, it doesn't mean that person has any idea what they are talking about. Just remember to stay civil and respectful when making your point.
Some of the best mainstream news outlets available also have excellent technology news departments, as well. Sites like the San Francisco Chronicle, situated in the heart of Silicon Valley, CNN, MSNBC and the BBC all have web pages with technology sections that are updated several times per day. It is always fun to read the same major breaking news story from more than one perspective, and the Internet allows you to do that without even batting an eyelash. Oftentimes, big tech news stories break through and end up on the main page for these sites so you won't even have to go looking for them.
Following in the footsteps of the major news agencies, the new kids on the block are also attempting to cover tech news. Sites like Yahoo News and Google News now have full time reporters on the beat and they regularly break stories that the other sites miss. This is a case of companies making so much money and having little idea of what to do with it, so they start their own news service. These sites are worth visiting, however, and you may read something you wouldn't have read in the old-fashioned press.
UMA Overview
With UMA, subscribers obtain a conformable individual undergo for their ambulatory vocalise and accumulation services as they transformation between networks. In visit to encourage the distributed acceptation of UMA technology, a sort of directive companies within the wireless business have together matured a ordered of unstoppered specifications. These specifications are acquirable finished this Web site, and haw be utilised by vendors and carriers of wireless subject systems and applications to amend and deploy interoperable solutions.
In constituent to nonindustrial and maintaining the initial specifications, the involved companies are actively employed with the 3GPP standards methodicalness to ingest the specifications as the foundation for the utilization of a conventional standard.
How UMA Technology Works

- A ambulatory client with a UMA-enabled, dual-mode phone moves within arrange of an unauthorized wireless meshwork to which the phone is allowed to connect.
- Upon connecting, the phone contacts the UMA Network Controller (UNC) over the band IP admittance meshwork to be genuine and commissioned to admittance GSM vocalise and GPRS accumulation services via the unauthorized wireless network.
- If approved, the subscriber’s underway positioning guidance stored in the set meshwork is updated, and from that saucer on every ambulatory vocalise and accumulation reciprocation is routed to the phone via the Unlicensed Mobile Access Network (UMAN) kinda than the cancellated broadcasting admittance meshwork (RAN).
- ROAMING: When a UMA-enabled client moves right the arrange of an unauthorized wireless meshwork to which they are connected, the UNC and phone assist roaming backwards to the licensed exterior network. This roaming impact is completely straight to the subscriber.
- HANDOVER: If a client is on an astir GSM vocalise call or GPRS accumulation conference when they become within arrange (or discover of range) of an unauthorized wireless network, that vocalise call or accumulation conference be able to automatically handover between admittance networks with no discernable assist interruption. Handovers are completely straight to the subscriber.



















